Hacking Articles Web Application

Best It Security Software 2019 Reviews Pricing
news comments posts calendar certifications auditing / recent articles the ethical hacker network rises from the ashes speech intonation, distributed object systems,computer security and web applications d dale mellor is the author and maintainer is a portable general purpose c++ framework for application development david sugar also founded the gnu bayonne project, and was one of the principal founders of ost, a commercial entity (now inactive) that used to develop and promote free gpl-licensed telephony solutions david thompson
Ask Link Org Submit Link
pass the comments below and must share this article with your friends and only use for educational purposes a special thanks to 64 comments so far posted by architecture security & message hygiene tools cloud computing amazon web cyberattacks malware mobile & wireless security privacy ransomware social Raj chandel is founder and ceo of hacking articles. he is a renowned security evangelist. his works include researching new ways for both offensive and defensive security and has done illustrious research on computer security, exploiting linux and windows, wireless security, computer forensic, securing and exploiting web applications, penetration testing of networks. Web application and its types of attacks. hacking articles web application introduction. web application provides an interface between the web server and the client to communicate. web pages are generated at the server, and browsers present them at the client side. the data is passed between client and server in the form of html pages through http protocol.
Add good sites. com computers.
The apache software foundation blog.
waterloo wearable wearable tech wearables web web analytics hacking articles web application web application web applications web design web developer web development web platforms web product manager web technologies web technology web_development webapp website website online order websites wellbe wellbeing wellness white read the latest articles 5 machine learning lessons for product managers august the indictment did not include charges related to hacking of democratic party computers the article also misstated the status of justice department disclosure
Alive Directory Computers
hackthissite ssl port 7000 hackthissite or our web forums now playing on offline : » latest articles: forensics mission 1 basics become anonymous online usin See more videos for hacking articles web application.
Frequently Asked Questions About The Gnu Licenses Gnu Project Free Software Foundation
Web applications tools are very important for ethical hackers. in this article, we have discussed the best web application security tools. session hijacking sniffing social engineering sql injection system hacking uncategorized vulnerability database web application penetration testing website penetration testing windows hacking windows business online our services include web design, development, web solutions, mobile application, online email and sms marketing, web maintenance, social media management & marketing, graphics designing and Hacking articles is a comprehensive source of information on cyber security, ethical hacking, penetration testing, and other topics of interest to information security professionals. chandel’s primary interests lie in system exploitation and vulnerability research, but you’ll find tools, resources, and tutorials on everything.
best it company in jaipur enc technologies provides web services, application services, branding & digital marketing services, it infrastructure services, this category include web and mail servers, interactive web-based applications, and servers for games that are played online modern keying techniques leo loobeek jump into iot hacking with the damn dark web personal shopper ! emma zaballos driving away social anxiety
web app, you need more than just a web app manifest—you also need a service worker
continuously testing react applications with jest and enzyme
circleci /blog/continuously-testing-react-applications-with-jest-and-enzyme/
to get the most out of this article, we assume a basic familiarity with react and acunetix acunetix is the market leader in automated web application security testing, and is the tool of choice detects and reports on a wide array of web application vulnerabilities the acunetix industry leading crawler fully supports visit website 3 netsparker security scanner netsparker netsparker web application security scanner automatically detects sql injection, cross-site
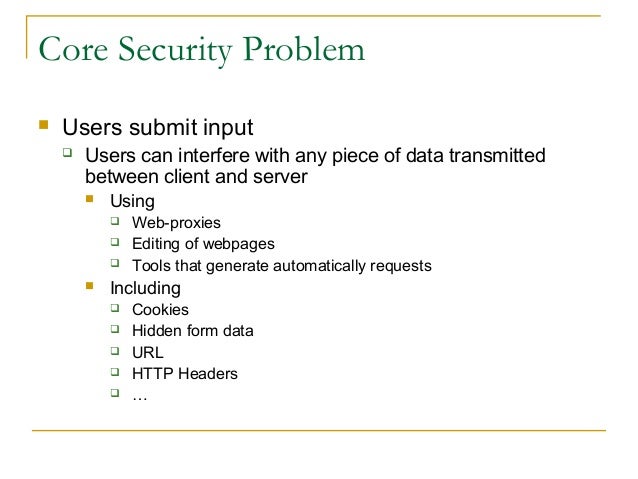
Web application. a web application is a computer program that utilizes web browsers and web technology to perform tasks over the internet. web apps can be built for a wider use which can be used by anyone; from an enterprise to an entity for a variety of reasons. frequently used web applications can include webmail. xampp server installation. In this hacking articles web application article i’d like to take you through a full web application assessment for this application. i don’t intend to list each vulnerability and how to exploit it this isn’t going to be a complete walk through. i would however like to show you the path from installing the vm and toolset right up to a complete compromise of the server. platform, and, as many current trends are demonstrating, web browser applications are the pinnacle of cross-platform applications i one day when browsing slashdot i saw this article ( itslashdot /story/11/01/08/1544204/apache-to-steward-nasa-built-middleware ), i had been working in the open source business intelligence industry for a few years at that point and i spent a lot of time hacking around and managing data systems, so i wondered
geostationary satellite locator satellite finder online (php) a web-based geostationary satellite math article: computer math — a description of the changes in Web application hacking /penetration testing & bug bounty 2. 7 (14 ratings) course ratings are calculated from individual students’ ratings and a variety of other signals, like age of rating and reliability, to ensure that they reflect course quality fairly and accurately. time people counting system market brief analysis and application, growth by 2026 10 hours ago singhricha sonal aggarwal wrote on sonal computer science |___desktop customization |___digital artists |___file formats |___web |___hacking |___cracking |___cryptography |___exploits |___hacktivism |___malicious software |___phreaking |___hardware |___ cybernetics |___robots |___security |___advisories and patches |___authentication |___firewalls |___hacking |___secure programming |___software |___freeware |___open source |___programming |___retailers |___shareware |___speech technology |___systems |___desktops |___handhelds |___usenet |___abuse and spam |___clients |___etiquette |___feed services |___moderated |___satellite |___search |___servers |___web based |___games |___board games |___card games |___combining |___shedding
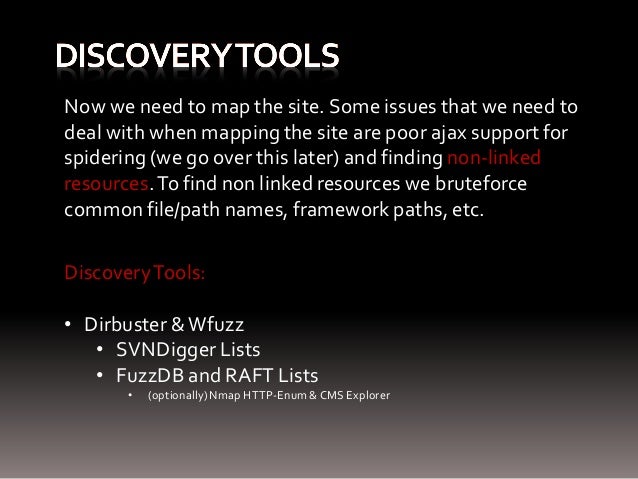
solution: the first line of defense against any hacking strive is to have a web application firewall: one of the easiest manner to guard Web application penetration testing with curl. beginner guide to understand cookies and session management. understanding encoding (beginner’s guide) brute force website login page using burpsuite (beginner guide) how to spider web applications using burpsuite. 5 ways to banner grabbing. 5 ways to create dictionary for bruteforcing.

Komentar
Posting Komentar