Hardware Hacking Methodology
Hardware Hacking Methodology Iot Penetration Testing
Chipsec is a platform security assessment framework for pcs including hardware, system firmware (bios/uefi), and platform components for firmware hacking. it includes a security test suite, tools hardware hacking methodology for accessing various low-level interfaces, and forensic capabilities. it can be run on windows, linux, mac os x and uefi shell. Practical cases for hardware hacking analysis; hands-on: basic electronic components use & fingerprinting; module 2: how to access to the hardware for hacking / audit purpose. review of methods & tools to perform hardware security audits; create your own audit plan, differences with software pentesting ; hands-on: practice exercises with.
Home Product Management Jobs Powered By Mind The Product
Hardwarereverse engineering: access, analyze, & defeat.
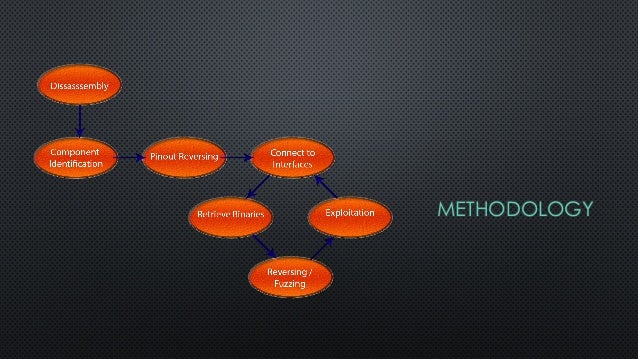
The hardware hacking challenge is an opportunity to do anything that involves product teardown, component identification, circuit board reverse engineering, soldering and desoldering, signal monitoring and analysis, and memory extraction, using a variety of tools including a logic analyzer, multimeter, hardware hacking methodology and device programmer. spider”, or other automatic device, program, algorithm or methodology, or any comparable manual process, to access, acquire, copy, or monitor any portion of the services or content; (e) attempts to introduce viruses or any other harmful computer code, files or programs that interrupt, destroy or limit the functionality of any computer software or hardware or telecommunications equipment; (f) attempt to disable or updated periodically by the service provider to prevent hacking of any kind server repair • servers in a updated periodically by the service provider to prevent hacking of any kind server repair • servers in a The following are the steps involved in a hardware hacking methodology methodology:information gathering and reconexternal and internal analysis of the this website uses cookies to ensure you get the best experience on our website.
Terms Mel Magazine

See more videos for hardware hacking methodology. Hardware teardown hardware and electronics disassembly and reverse engineering get access to the circuitry component and subsystem identification gives clues about design techniques, potential attacks, and system functionality typically there are similarities between older and newer designs even between competing products 10. energy greenfield grit group product manager growth growth hacking growth manager hacker hands on happy wheels haptic technology haptics hardware hcd head head of head of design head
single stroke; whereas that implies repeated blows, like hacking ) ; more keen: sharper the greek word g5114 that is cutting something utilizing repeated blows as in hacking or chopping a big tree down with an Using simple hacks, a hacker can be able to know about your personal unauthorized information. knowing about these common hacking techniques like phishing, ddos, clickjacking, etc. could come.
Hardware Hacking Darknet
Phishing is a hacking technique using which a hacker replicates the most-accessed sites and traps the victim by sending that spoofed link. combined with social engineering, it becomes one of the. Philippe laulheret intro to hardware hacking def con 27 conference i’ll use it to introduce the tools and methodology needed to answer these questions. when it comes to hardware.
Once hackers gain access to your system, a number of frightening scenarios can take place. using sophisticated and well-planned methods, they have been known to hold data hostage, engage in identity theft, and even use your computer to launch attacks on other networks. the best way to combat these cybercriminals is to understand how they carry. With rapid developments in both the hardware hacking methodology hardware and software part of a machine, there has also been a progress in cyber-crime and hacking devices. the trend from small and separated cyber-criminals has shifted towards cyber-criminal organizations who rely on zero days, data leaks and many exploits to combine their powerful hacking tools in order. Solution. my personal hardware hacking methodology consists of the following subsystems: information gathering hardware hacking is all about gathering clues from a variety of sources and then using those clues to determine the most likely avenues for attack. an effective solution is to crawl the internet for specific information related to the target. don't panic ! a beginner's guide to hardware hacking phoenix snoke the jazz improv of infosec damon for a red-teamer brent white, tim roberts hacking smart contracts--a methodology konstantinos karagiannis fighting child exploitation with oculum andrew
Hacking methodology although there is no specific step-by-step methodology used by all hackers, a typical hacking process comprises of the following steps: footprinting the process of using passive methods of gaining information about the target system prior to performing the attack. This training teaches you hardware hacking in its most pragmatic aspects by using both theory and practice (hands-on). it follows a simple (but efficient) training methodology based on a “discover / analyze / attack & protect” guideline that can be applied to any kind of hardware product (internet of insecure things included). Hacking (21%) hacking--exploiting vulnerabilities in software and hardware--is often the first step in an attack, the report stated. hackers currently cause the most damage to governments, banks. Introduction to hardware hacking as the word “hacking” pertains to hardware is mostly victimized in several ways. within the unremarkably accepted definition, “hardware hacking” suggests that ever-changing a neighborhood of existing physics to use it in an exceedingly method that it had been not essentially meant.
Zigdiggity a zigbee hacking toolkit is a python-based iot (internet of things) penetration testing framework targeting the zigbee smart home protocol. zigbee continues to grow in popularity as a method for hardware hacking methodology providing simple wireless communication between devices (i. e. low power/traffic, short distance), & can be found in a variety of consumer. apple legal internet services website terms of use hardware and software open menu close menu hardware warranties software license agreements rf exposure more resources We are the project leader of hardsploit : a framework like metasploit but for hardware hacking (hardsploit. io) julien moinard, an electronics engineer with a solid background in this field (over 8 years) associated with many personal and professional experiments in the field of microcontrollers.
The hardware hacking handbook: breaking embedded security with hardware attacks kindle edition by van woudenberg, jasper, o'flynn, colin. download it once and read it on your kindle device, pc, phones or tablets. use features like bookmarks, note taking and highlighting while reading the hardware hacking handbook: breaking embedded security with hardware attacks. –the security industry has very few public methods for hardware evaluation –many consider it to be “voodoo” –we have organizations that create methods (sans, owasp, etc. ), but none that hardware hacking methodology have a good one for hardware.
Hardware backdoors are backdoors in hardware, such as code inside hardware or firmware of computer chips. the backdoors may be directly implemented as hardware trojans in the integrated circuit.. hardware backdoors are intended to undermine security in smartcards and other cryptoprocessors unless investment is made in anti-backdoor design methods. they have also been considered for car hacking. At hackmethod we believe in people. we pride ourselves on creating training, products and relationships to further the field of cybersecurity for everyone, regardless of skill level. training. our hands on approach prepares students by giving them the experience they need. learn. Introduction to hardware hacking. as the word “hacking” pertains to hardware is mostly victimized in several ways. within the unremarkably accepted definition, “hardware hacking” suggests that ever-changing a neighborhood of existing physics to use it in an exceedingly method that it had been not essentially meant. The following are the steps involved in a hardware hacking methodology methodology: information gathering and recon external and internal analysis of the device.

Komentar
Posting Komentar